Image Catalog
The Image Catalog lists all container images available through Root Image Catalog atcr.root.io. Access it at app.root.io/images/catalog.
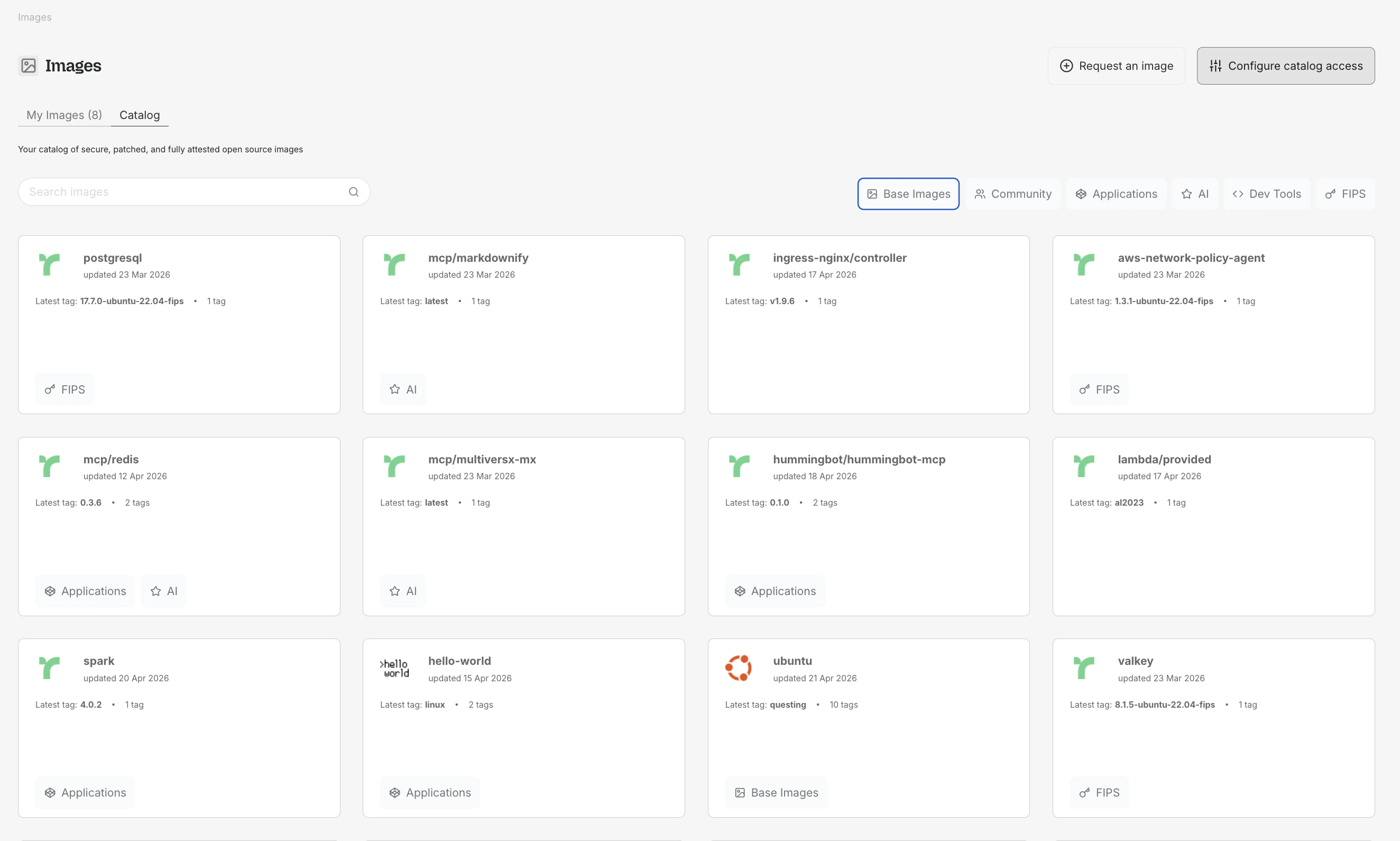
What you see
The catalog displays images that have active subscriptions. Each image card shows:- Image name (e.g.,
python,node,postgres) - Available tags with architecture indicators (amd64, arm64)
- Vulnerability reduction chart - a before/after comparison of Critical and High CVEs between the upstream image and Root’s patched version
Images that are not actively subscribed by any customer may not appear in the public catalog. Any image can be added within 48 hours upon request — contact Root at root.io/contact.
Subscribing to an image
Select a tag
Click the image to view available tags. Choose the tag matching your current usage (e.g.,
3.11-slim-bookworm).Subscribe
Click Subscribe on the tag. Root begins scanning for vulnerabilities and generating patched versions.
Vulnerability charts
Each image tag page includes a before/after vulnerability chart showing how Root reduces Critical and High CVEs over time. The chart plots counts across successive scans so you can see the remediation trend.For images based on older distributions (e.g., Debian Bullseye, Amazon Linux), Root may not achieve zero vulnerabilities because backports are not always available. The chart indicates when this is the case.
Architecture support
Root images are available for bothamd64 and arm64. The catalog shows which architectures are available for each tag. Docker automatically selects the correct architecture when pulling.
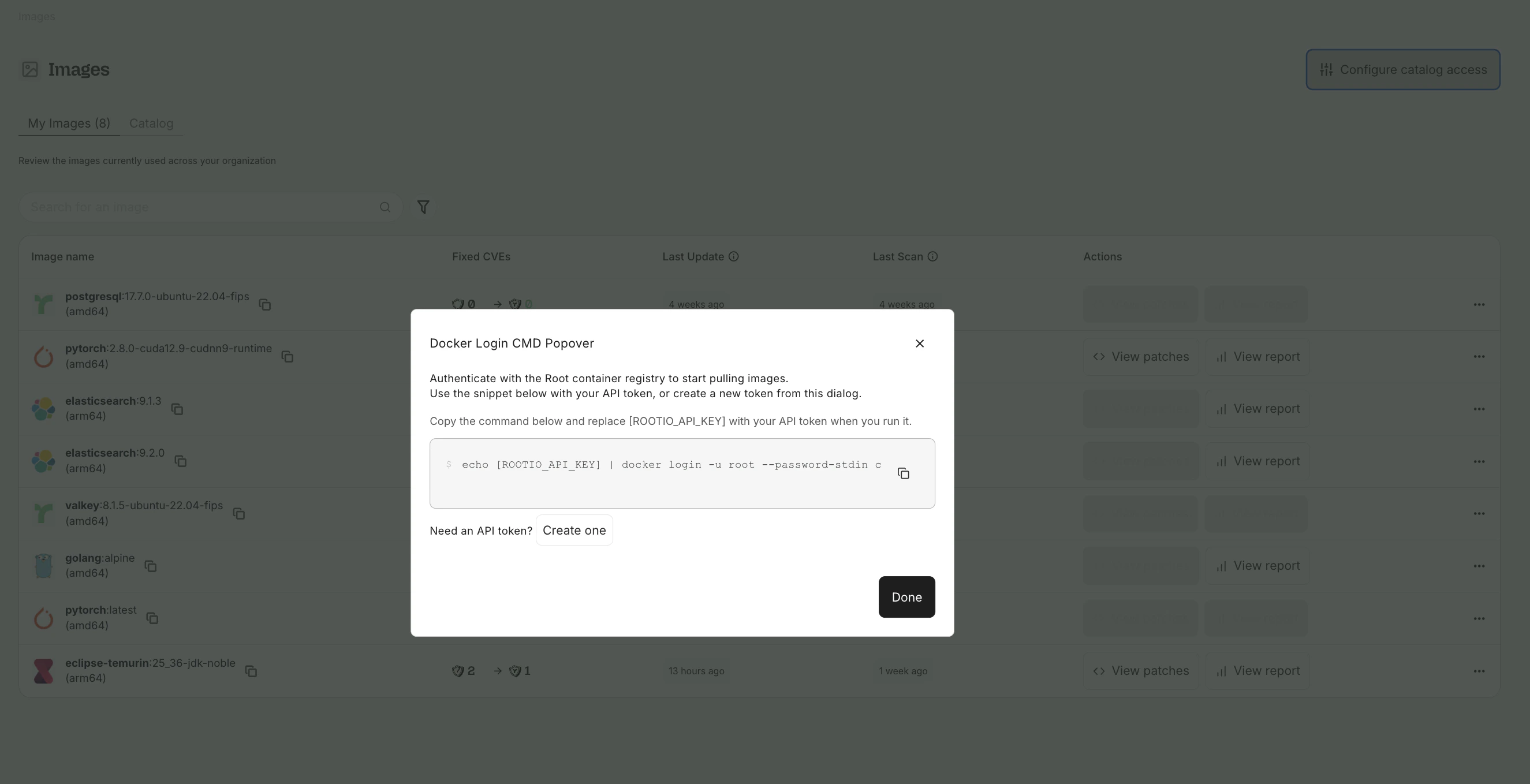
My Images
My Images shows the images your organization is currently subscribed to.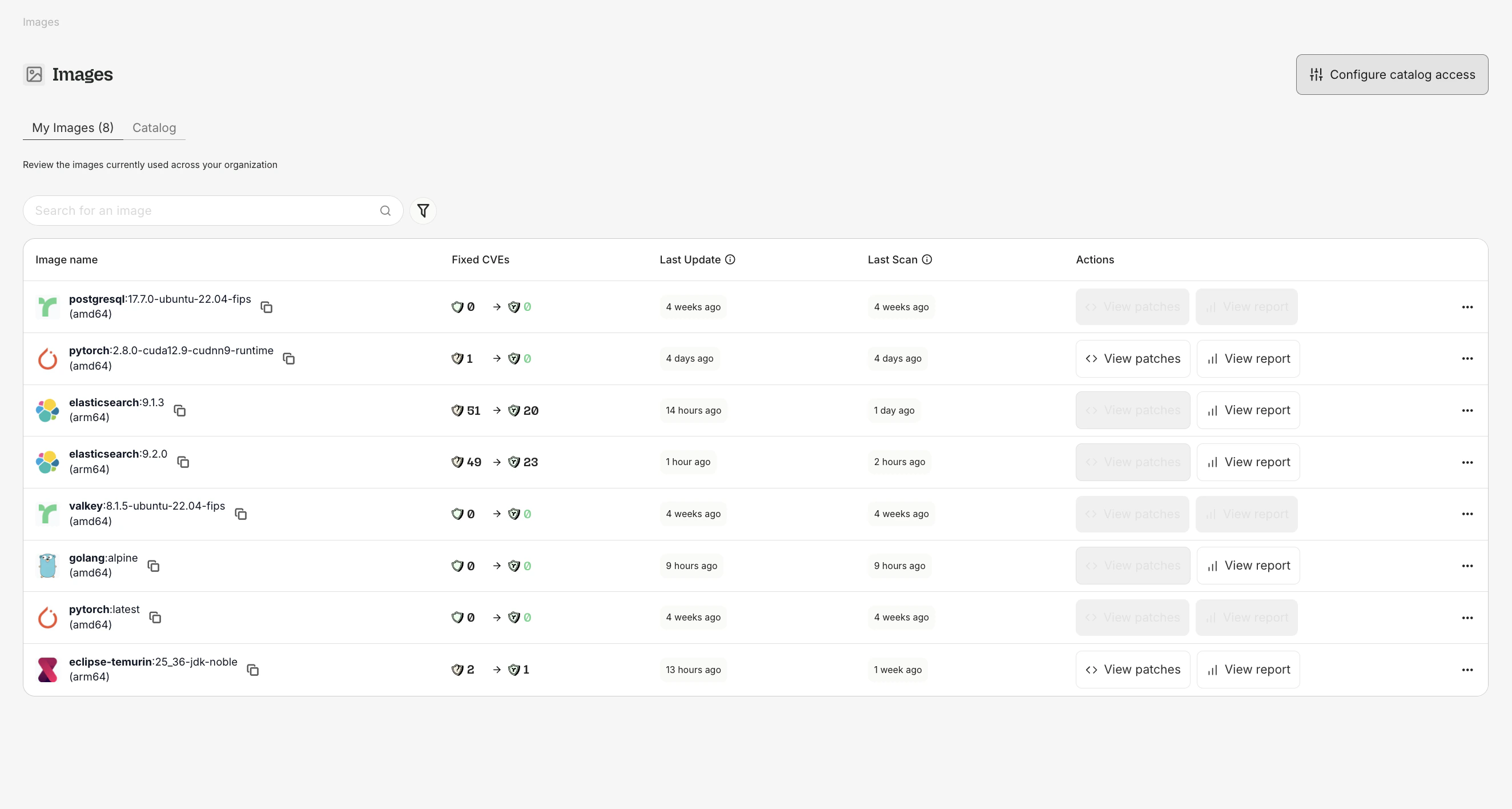
What you see
| Column | Description |
|---|---|
| Image:Tag | The image name and tag |
| Architecture | amd64, arm64, or both |
| Before | Critical + High CVE count in the upstream image |
| After | Critical + High CVE count in Root’s patched version |
| Status | Whether the image is up to date, pending scan, or has issues |
Image reports
Click View Report on any subscribed image to open the Image Report:- Vulnerability breakdown by severity (Critical, High, Medium, Low)
- Security Findings table listing each finding with status, severity, and SLA information
- Before/after chart showing remediation progress over time
- Package details for every OS package in the image
FIPS images
Root offers FIPS 140-3 validated images for regulated environments, identified with a FIPS badge in the catalog. See FIPS Images for details.Pulling Root images