wizcli docker scan to compare the vulnerability posture of any upstream image against its Root-patched equivalent.
Prerequisites
wizcliinstalled and authenticated — see Wiz CLI docs- Root registry credentials — see Authentication
Scanning Root images
Pass anycr.root.io image reference directly to wizcli docker scan:
Before and after Root
The example below scansnode:25.0.0 from Docker Hub alongside its Root equivalent.
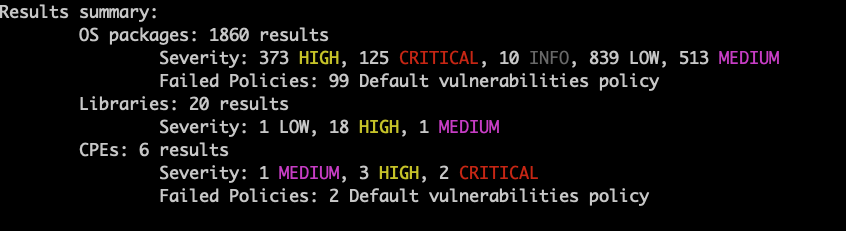
Upstream (Docker Hub):
cr.root.io):
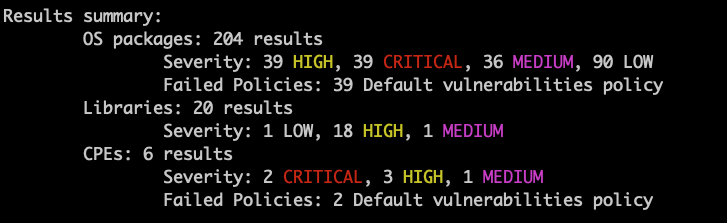
| node:25.0.0 (Docker Hub) | cr.root.io/node:25.0.0 (Root) | |
|---|---|---|
| OS packages found | 1,860 | 204 |
| CRITICAL | 125 | 39 |
| HIGH | 373 | 39 |
| MEDIUM | 513 | 36 |
| LOW | 839 | 90 |
| Failed policies (OS) | 99 | 39 |
CI/CD
Add a scan step to your pipeline to gate on policy failures: GitHub Actions:Troubleshooting
| Issue | Solution |
|---|---|
401 Unauthorized pulling from cr.root.io | Verify your Root token is valid — see Authentication |
wizcli not authenticated | Run wizcli auth and confirm your Wiz credentials are set |
| Scan returns no results | Confirm the image was pulled successfully before scanning |